
What can you do if someone is using your personal email address? If your family and friends get suspicious mails from your address, you might think you’ve been hacked. Similarly, if you get spam from someone you know, has their system been compromised?
This is a process called email spoofing. It’s surprisingly simple to do and incredibly common.
What Is Email Spoofing?
Your immediate concern is, of course, that you’ve become a victim of cybercriminals. However, this often isn’t the case; instead, someone is faking your email address.
All emails come with details of the recipient and the sender, and the latter can be spoofed (which simply means it’s an imitation address).
So why have you received an email seemingly from yourself? There are a few possibilities.
The first instance is when a message can’t be delivered, so is “returned” to the address in the sender field. This will seem especially odd if you didn’t send that message. At least you now know that someone is faking your address.
Scammers can learn of your address through numerous methods, including social media accounts and mutual contacts. It could also be that your email address is in the public domain anyway; if you’re a business or have a newsletter, for instance, your address will probably be publicized. This makes life a lot easier for scammers looking to spoof emails.
Many of us send ourselves important documents and images through email as a means to back them up. This is a simple way of keeping your vital files accessible wherever you are, without the need for cloud computing.
Cybercriminals see this as an opportunity: an email from yourself or another contact may sufficiently pique your curiosity and you’ll click on the enclosed link.
And we all know not to trust links in emails, right? This is how viruses spread and gain private data about users. It’s one way scammers can get past whatever security measures you’ve taken. By clicking a link, you’re essentially accepting a download of any software enclosed, which bypasses even the sandboxing process your browser uses to keep your device safe.
How Are Email Addresses Spoofed?

So how does it work? How can you spoof, and subsequently spam, an email address?
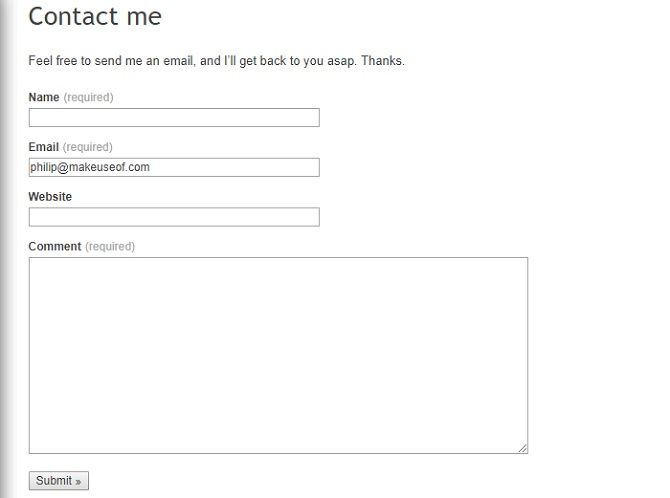
All a scammer needs is a Simple Mail Transfer Protocol (SMTP) server—that is, a server that can send emails—and the right mailing equipment. This could simply be Microsoft Office Outlook.
You need to provide a display name, email address, and login information: basically, a username and password. The latter lets you into your own email account, but your displayed name and email address can actually be whatever you like.
Code libraries like PHPMailer streamline the process; you simply have to fill out the “From” field, write your message, and add in the recipient’s address.
We don’t advise you do this, obviously, because, depending on your jurisdiction, it’s illegal.
Most email clients don’t support the practice. They typically ask you to verify that you can log into the address you’re pretending to send messages from.
There are ways around this, but scammers bypass it using “botnets” as mail servers. A botnet is a system of infected computers, acting generally without the users’ knowledge to forward viruses, spam, and worms to other devices.
Why Did Strangers Get Emails From Me?
In rare cases, you might get an angry message from a stranger who claims you sent them a virus. Yep, this is due to email spoofing.
When one machine is compromised, malicious software scours the address book and sends malicious software to contacts using that email client. These often claim to be from a friend of the infected computer’s user.
You don’t even need to know this person—their name is being used solely because you have a mutual contact!
A virus’ modus operandi is to prosper. They spread and infect as many machines as possible to gain as much personal information, and therefore influence, as they can. Most notably, this is through malware installed on a device through subterfuge, like a Trojan horse which purports to be something useful while hoovering up your data.
If you get a message from an irate stranger, explain that this isn’t your fault. Maybe forward them onto this page so they’re aware of what can be done. You could then try to isolate which contact you’ve got in common, so you can alert them that their system has been compromised. That’s a bit of a needle in a haystack, however…
What to Do If You Get a Suspicious Email
If there’s a link in the email, do not click it. Similarly, don’t download any attachments unless you know they’re genuine. It doesn’t matter if it comes from someone you think you can trust or not.
Read up on spotting a fake email, and don’t ignore basic practices if the email is supposedly from someone you know. We tend to be immediately skeptical of out-of-the-blue mails from our own address, but not of unsolicited messages from friends.
Then again, the fact that you know the sender should give you an advantage. You know if they’re likely to send a link on its own with no other text around it; whether their messages are long and rambling; or whether they always make spelling mistakes.
If nothing’s immediately obvious, check through previous emails and note patterns. Do they have a signature that comes through on all their messages? Do they normally send emails via their phone, and so have “Sent from my iPhone”, for example, at the bottom?
If you’re still not sure, simply ask the supposed sender.
What to Do If Someone Is Using Your Email Address

We always advise you not to click on anything you think might be malicious. Certainly don’t click on anything if the email appears to be from your own address and you don’t recall sending it.
If the message claims to be from you, check your Sent folder. If it’s there, but you didn’t send it, your account has likely been compromised. Equally, if you look on Gmail, you can see “Last Account Activity”, which might give you an indication about whether someone else is logging into your account.
You must change your password straight away. Check out these tips for creating a stronger password.
Unfortunately, there’s very little you can do about spoofing, apart from become more savvy about spam.
But you need not feel entirely useless because you might be able to ascertain the Internet Protocol (IP) address from an email. You can trace the origin of email by learning to open headers and finding the IP address. This might look intimidating, but from there, you can then trace that to a PC.
Someone tried to use my spam email and a fake name to trick me into paying for their apple stuff. Yeah cuz I totally signed up as "Jay Moe"— jmo (@jmonumber3) April 16, 2016
It can be a frustrating situation to find yourself in, but fortunately, more people recognize email spoofing as a scam, immediately sending such items to the trash.
They do serve as a timely reminder that we always need to keep every aspect of our online lives secure—that means social media feeds, your browsers, and your email accounts. You can at least switch to an encrypted provider that knows the importance of privacy.

No comments:
Post a Comment